Top suggestions for SECURITYExplore more searches like SECURITY |
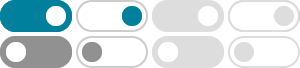
- Image size
- Color
- Type
- Layout
- People
- Date
- License
- Clear filters
- SafeSearch:
- Moderate
- Security Methods
- Security
Threat Protection - Network
Security Methods - Data
Security Methods - Methods
of Securing - Method of Protection
Against Security - Methods
of Protecting Data - Methods
for Internet Security - Protection Methods
of Cyber Security - Data Protection
Techniques - Network Security
Controls - Using All
Security Methods - Protection Methods Security
and Safety - Computer
Protection Methods - Site
Security Methods - Instrument Methods
of Protection - Physical
Protection Methods - Methods
of Electrial Protection - External Interface
Protection in Security - System and Data
Security - Difference Between
Protection and Security - Radiation
Protection Methods - Non-Physical
Methods of Protection - Security
Systems and Protection - Different Cyber
Security Methods - Security Protection
Available - Gparm
Security Protection - Protective
Security - Security and Protection
in It - Security Protection
Mechanism - Personal Information
Protection Methods - Security Protection
Screen Shot - Data Protection
Measures - Application
Security Methods - Hardware
Protection Methods - Protective Signaling and
Security - Compound
Security Protection - Secure and
Protection Management - Method of Protection
and Standards - Methods
of File Security - Diagrams of
Methods of Protection - Choice of
Security Method - Methods of Security
Respond TW - Security vs Protection
in OS - Methods
of Egnition Protection - Methods
of Ex Protection - Describe End User Device
Protection Methods - Components of OS
Security and Protection - Network Prevention
System - Security
for Proctection
 Related Products
Related Products
Some results have been hidden because they may be inaccessible to you.Show inaccessible results

 Feedback
Feedback